Good Neighbour Podcast with Jody Patfield of KIS Technologies Inc
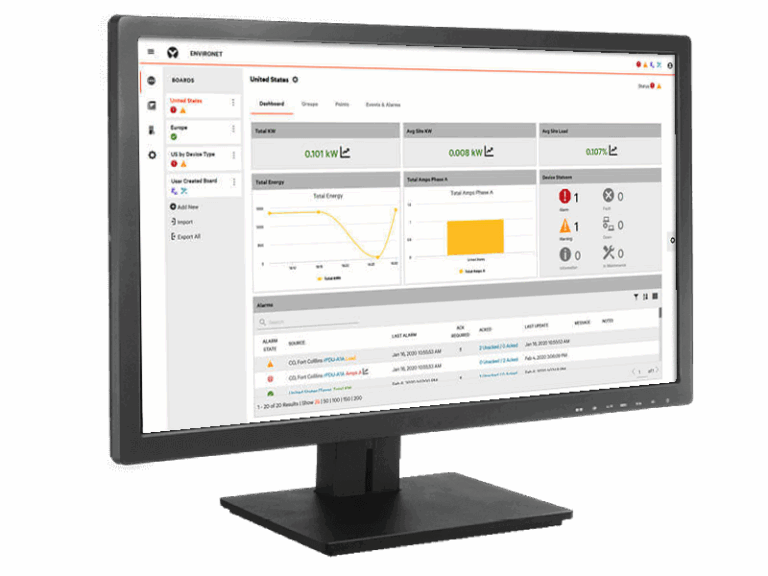
Celebrating our 26th year of providing Digital office equipment such as photocopiers, printers, scanners and phone systems to local Businesses. Our business has expanded over the years, and now includes our Managed IT Services/Security Department, which provides customized and reliable…